各位,如果你是 tecmint.com 的常規讀者,你會注意到這是我們關於安全工具的第三篇文章。在我們之前的兩篇文章中,我們已經為您提供了如何使用 mod_security 和 mod_evasive 以及 LMD(Linux Malware Detect)來保護 Apache 和 Linux 系統免受 Malware、DOS 和 DDOS 攻擊的所有指導。
我們再次在這裡介紹一個名為 Rkhunter(Rootkit Hunter)的新安全工具。本文將指導您如何在 Linux 系統中使用源代碼安裝和配置 RKH(RootKit Hunter)。
什麼是 Rkhunter?
Rkhunter(Rootkit Hunter)是一個針對 Linux 系統的開源 Unix/Linux 掃描工具,釋出於 GPL 下,用於掃描系統中的後門、rootkits 和本地漏洞。
它掃描隱藏文件、二進制文件上設置的錯誤權限、核心中的可疑字符串等。要了解更多關於 Rkhunter 及其功能的信息,請訪問 http://rkhunter.sourceforge.net/。
在 Linux 系統中安裝 Rootkit Hunter 掃描器
第 1 步:下載 Rkhunter
首先,前往 Rkhunter 工具的官方网站 http://rkhunter.sourceforge.net/ 下载最新稳定版本,或者使用以下 Wget 命令在您的系统上下载它。
# cd /tmp # wget http://downloads.sourceforge.net/project/rkhunter/rkhunter/1.4.6/rkhunter-1.4.6.tar.gz
步骤 2:安装 Rkhunter
一旦您下载了最新版本,请以 root 用户身份运行以下命令来安装它。
# tar -xvf rkhunter-1.4.6.tar.gz # cd rkhunter-1.4.6 # ./installer.sh --layout default --install
示例输出
Checking system for: Rootkit Hunter installer files: found A web file download command: wget found Starting installation: Checking installation directory "/usr/local": it exists and is writable. Checking installation directories: Directory /usr/local/share/doc/rkhunter-1.4.2: creating: OK Directory /usr/local/share/man/man8: exists and is writable. Directory /etc: exists and is writable. Directory /usr/local/bin: exists and is writable. Directory /usr/local/lib64: exists and is writable. Directory /var/lib: exists and is writable. Directory /usr/local/lib64/rkhunter/scripts: creating: OK Directory /var/lib/rkhunter/db: creating: OK Directory /var/lib/rkhunter/tmp: creating: OK Directory /var/lib/rkhunter/db/i18n: creating: OK Directory /var/lib/rkhunter/db/signatures: creating: OK Installing check_modules.pl: OK Installing filehashsha.pl: OK Installing stat.pl: OK Installing readlink.sh: OK Installing backdoorports.dat: OK Installing mirrors.dat: OK Installing programs_bad.dat: OK Installing suspscan.dat: OK Installing rkhunter.8: OK Installing ACKNOWLEDGMENTS: OK Installing CHANGELOG: OK Installing FAQ: OK Installing LICENSE: OK Installing README: OK Installing language support files: OK Installing ClamAV signatures: OK Installing rkhunter: OK Installing rkhunter.conf: OK Installation complete
步骤 3:更新 Rkhunter
通过运行以下命令运行 RKH 更新程序来填充数据库属性。
# /usr/local/bin/rkhunter --update # /usr/local/bin/rkhunter --propupd
示例输出
[ Rootkit Hunter version 1.4.6 ] Checking rkhunter data files... Checking file mirrors.dat [ Updated ] Checking file programs_bad.dat [ No update ] Checking file backdoorports.dat [ No update ] Checking file suspscan.dat [ No update ] Checking file i18n/cn [ No update ] Checking file i18n/de [ No update ] Checking file i18n/en [ No update ] Checking file i18n/tr [ No update ] Checking file i18n/tr.utf8 [ No update ] Checking file i18n/zh [ No update ] Checking file i18n/zh.utf8 [ No update ] Checking file i18n/ja [ No update ] File created: searched for 177 files, found 131, missing hashes 1
步骤 4:设置定时任务和电子邮件提醒
在 /etc/cron.daily/ 下创建一个名为 rkhunter.sh 的文件,然后每天扫描您的文件系统并向您的电子邮件地址发送电子邮件通知。使用您喜欢的编辑器创建以下文件。
# vi /etc/cron.daily/rkhunter.sh
将以下代码添加到文件中,并将“YourServerNameHere”替换为您的“服务器名称”,将“[email protected]”替换为您的“电子邮件地址“。
#!/bin/sh ( /usr/local/bin/rkhunter --versioncheck /usr/local/bin/rkhunter --update /usr/local/bin/rkhunter --cronjob --report-warnings-only ) | /bin/mail -s 'rkhunter Daily Run (PutYourServerNameHere)' [email protected]
设置文件的执行权限。
# chmod 755 /etc/cron.daily/rkhunter.sh
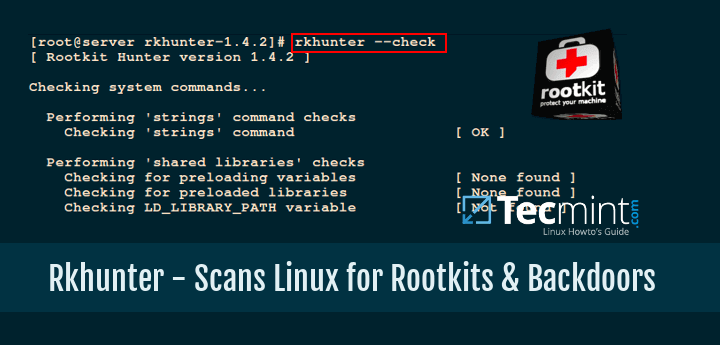
步骤 5:手动扫描和使用
要扫描整个文件系统,请以 root 用户身份运行 Rkhunter。
# rkhunter --check
示例输出
[ Rootkit Hunter version 1.4.6 ]
Checking system commands...
Performing 'strings' command checks
Checking 'strings' command [ OK ]
Performing 'shared libraries' checks
Checking for preloading variables [ None found ]
Checking for preloaded libraries [ None found ]
Checking LD_LIBRARY_PATH variable [ Not found ]
Performing file properties checks
Checking for prerequisites [ OK ]
/usr/local/bin/rkhunter [ OK ]
/usr/sbin/adduser [ OK ]
/usr/sbin/chkconfig [ OK ]
/usr/sbin/chroot [ OK ]
/usr/sbin/depmod [ OK ]
/usr/sbin/fsck [ OK ]
/usr/sbin/fuser [ OK ]
/usr/sbin/groupadd [ OK ]
/usr/sbin/groupdel [ OK ]
/usr/sbin/groupmod [ OK ]
/usr/sbin/grpck [ OK ]
/usr/sbin/ifconfig [ OK ]
/usr/sbin/ifdown [ Warning ]
/usr/sbin/ifup [ Warning ]
/usr/sbin/init [ OK ]
/usr/sbin/insmod [ OK ]
/usr/sbin/ip [ OK ]
/usr/sbin/lsmod [ OK ]
/usr/sbin/lsof [ OK ]
/usr/sbin/modinfo [ OK ]
/usr/sbin/modprobe [ OK ]
/usr/sbin/nologin [ OK ]
/usr/sbin/pwck [ OK ]
/usr/sbin/rmmod [ OK ]
/usr/sbin/route [ OK ]
/usr/sbin/rsyslogd [ OK ]
/usr/sbin/runlevel [ OK ]
/usr/sbin/sestatus [ OK ]
/usr/sbin/sshd [ OK ]
/usr/sbin/sulogin [ OK ]
/usr/sbin/sysctl [ OK ]
/usr/sbin/tcpd [ OK ]
/usr/sbin/useradd [ OK ]
/usr/sbin/userdel [ OK ]
/usr/sbin/usermod [ OK ]
....
[Press to continue]
Checking for rootkits...
Performing check of known rootkit files and directories
55808 Trojan - Variant A [ Not found ]
ADM Worm [ Not found ]
AjaKit Rootkit [ Not found ]
Adore Rootkit [ Not found ]
aPa Kit [ Not found ]
.....
[Press to continue]
Performing additional rootkit checks
Suckit Rookit additional checks [ OK ]
Checking for possible rootkit files and directories [ None found ]
Checking for possible rootkit strings [ None found ]
....
[Press to continue]
Checking the network...
Performing checks on the network ports
Checking for backdoor ports [ None found ]
....
Performing system configuration file checks
Checking for an SSH configuration file [ Found ]
Checking if SSH root access is allowed [ Warning ]
Checking if SSH protocol v1 is allowed [ Warning ]
Checking for a running system logging daemon [ Found ]
Checking for a system logging configuration file [ Found ]
Checking if syslog remote logging is allowed [ Not allowed ]
...
System checks summary
=====================
File properties checks...
Files checked: 137
Suspect files: 6
Rootkit checks...
Rootkits checked : 383
Possible rootkits: 0
Applications checks...
Applications checked: 5
Suspect applications: 2
The system checks took: 5 minutes and 38 seconds
All results have been written to the log file: /var/log/rkhunter.log
One or more warnings have been found while checking the system.
Please check the log file (/var/log/rkhunter.log)
以上命令會在/var/log/rkhunter.log生成一個日誌文件,其中包含由Rkhunter進行的檢查結果。
# cat /var/log/rkhunter.log
樣本輸出
[11:21:04] Running Rootkit Hunter version 1.4.6 on tecmint [11:21:04] [11:21:04] Info: Start date is Mon Dec 21 11:21:04 AM IST 2020 [11:21:04] [11:21:04] Checking configuration file and command-line options... [11:21:04] Info: Detected operating system is 'Linux' [11:21:04] Info: Found O/S name: Fedora release 33 (Thirty Three) [11:21:04] Info: Command line is /usr/local/bin/rkhunter --check [11:21:04] Info: Environment shell is /bin/bash; rkhunter is using bash [11:21:04] Info: Using configuration file '/etc/rkhunter.conf' [11:21:04] Info: Installation directory is '/usr/local' [11:21:04] Info: Using language 'en' [11:21:04] Info: Using '/var/lib/rkhunter/db' as the database directory [11:21:04] Info: Using '/usr/local/lib64/rkhunter/scripts' as the support script directory [11:21:04] Info: Using '/usr/local/sbin /usr/local/bin /usr/sbin /usr/bin /bin /sbin /usr/libexec /usr/local/libexec' as the command directories [11:21:04] Info: Using '/var/lib/rkhunter/tmp' as the temporary directory [11:21:04] Info: No mail-on-warning address configured [11:21:04] Info: X will be automatically detected [11:21:04] Info: Found the 'basename' command: /usr/bin/basename [11:21:04] Info: Found the 'diff' command: /usr/bin/diff [11:21:04] Info: Found the 'dirname' command: /usr/bin/dirname [11:21:04] Info: Found the 'file' command: /usr/bin/file [11:21:04] Info: Found the 'find' command: /usr/bin/find [11:21:04] Info: Found the 'ifconfig' command: /usr/sbin/ifconfig [11:21:04] Info: Found the 'ip' command: /usr/sbin/ip [11:21:04] Info: Found the 'ipcs' command: /usr/bin/ipcs [11:21:04] Info: Found the 'ldd' command: /usr/bin/ldd [11:21:04] Info: Found the 'lsattr' command: /usr/bin/lsattr ...
有關更多信息和選項,請運行以下命令。
# rkhunter --help
如果您喜歡本文,那麼分享是表達感謝的正確方式。
Source:
https://www.tecmint.com/install-rootkit-hunter-scan-for-rootkits-backdoors-in-linux/













